Requirements¶
Prowler has been written in Python using the AWS SDK (Boto3), Azure SDK and GCP API Python Client.
AWS¶
Since Prowler uses AWS Credentials under the hood, you can follow any authentication method as described here.
Authentication¶
Make sure you have properly configured your AWS-CLI with a valid Access Key and Region or declare AWS variables properly (or instance profile/role):
or
export AWS_ACCESS_KEY_ID="ASXXXXXXX"
export AWS_SECRET_ACCESS_KEY="XXXXXXXXX"
export AWS_SESSION_TOKEN="XXXXXXXXX"
Those credentials must be associated to a user or role with proper permissions to do all checks. To make sure, add the following AWS managed policies to the user or role being used:
arn:aws:iam::aws:policy/SecurityAuditarn:aws:iam::aws:policy/job-function/ViewOnlyAccess
Note
Moreover, some read-only additional permissions are needed for several checks, make sure you attach also the custom policy prowler-additions-policy.json to the role you are using. If you want Prowler to send findings to AWS Security Hub, make sure you also attach the custom policy prowler-security-hub.json.
Multi-Factor Authentication¶
If your IAM entity enforces MFA you can use --mfa and Prowler will ask you to input the following values to get a new session:
- ARN of your MFA device
- TOTP (Time-Based One-Time Password)
Azure¶
Prowler for Azure supports the following authentication types:
- Service principal authentication by environment variables (Enterprise Application)
- Current az cli credentials stored
- Interactive browser authentication
- Managed identity authentication
Service Principal authentication¶
To allow Prowler assume the service principal identity to start the scan it is needed to configure the following environment variables:
export AZURE_CLIENT_ID="XXXXXXXXX"
export AZURE_TENANT_ID="XXXXXXXXX"
export AZURE_CLIENT_SECRET="XXXXXXX"
If you try to execute Prowler with the --sp-env-auth flag and those variables are empty or not exported, the execution is going to fail.
AZ CLI / Browser / Managed Identity authentication¶
The other three cases does not need additional configuration, --az-cli-auth and --managed-identity-auth are automated options. To use --browser-auth the user needs to authenticate against Azure using the default browser to start the scan, also tenant-id is required.
Permissions¶
To use each one you need to pass the proper flag to the execution. Prowler for Azure handles two types of permission scopes, which are:
- Microsoft Entra ID permissions: Used to retrieve metadata from the identity assumed by Prowler (not mandatory to have access to execute the tool).
- Subscription scope permissions: Required to launch the checks against your resources, mandatory to launch the tool.
Microsoft Entra ID scope¶
Microsoft Entra ID (AAD earlier) permissions required by the tool are the following:
Directory.Read.AllPolicy.Read.AllUserAuthenticationMethod.Read.All
The best way to assign it is through the Azure web console:
- Access to Microsoft Entra ID
- In the left menu bar, go to "App registrations"
- Once there, in the menu bar click on "+ New registration" to register a new application
- Fill the "Name, select the "Supported account types" and click on "Register. You will be redirected to the applications page.
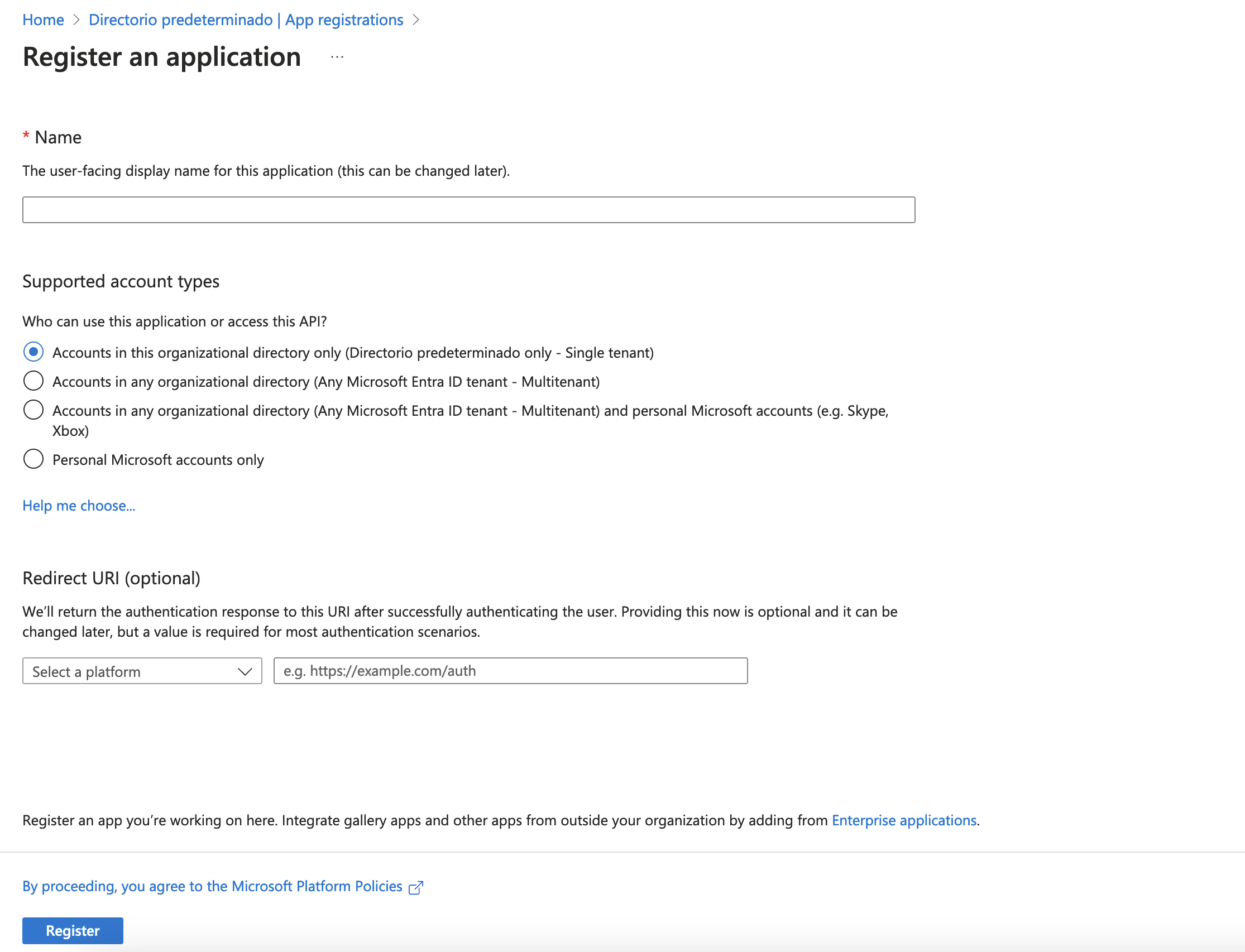
- Select the new application
- In the left menu bar, select "API permissions"
- Then click on "+ Add a permission" and select "Microsoft Graph"
- Once in the "Microsoft Graph" view, select "Application permissions"
- Finally, search for "Directory", "Policy" and "UserAuthenticationMethod" select the following permissions:
Directory.Read.AllPolicy.Read.AllUserAuthenticationMethod.Read.All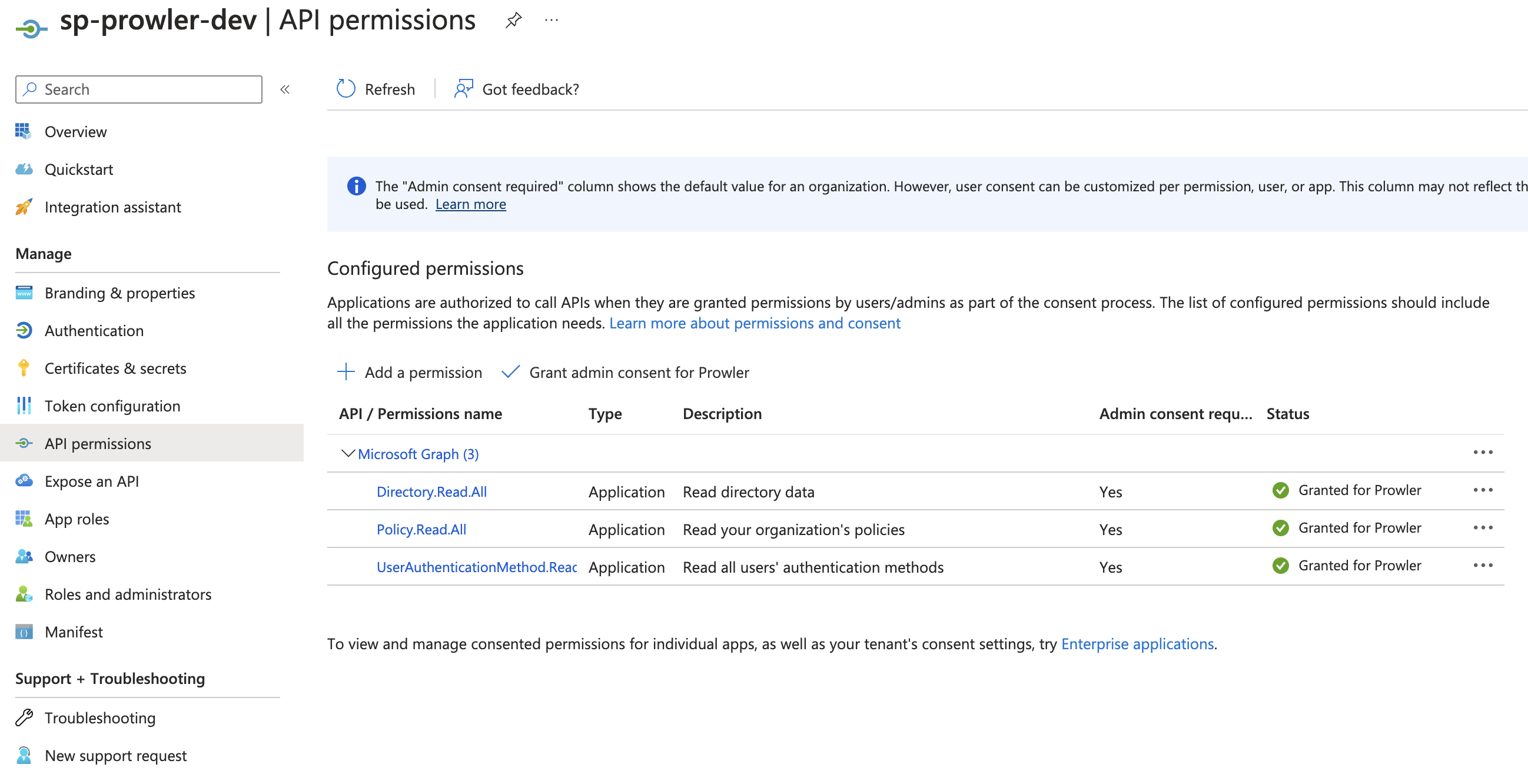
Subscriptions scope¶
Regarding the subscription scope, Prowler by default scans all the subscriptions that is able to list, so it is required to add the following RBAC builtin roles per subscription to the entity that is going to be assumed by the tool:
Security ReaderReader
To assign this roles, follow the instructions:
- Access your subscription, then select your subscription.
- Select "Access control (IAM)".
- In the overview, select "Roles"
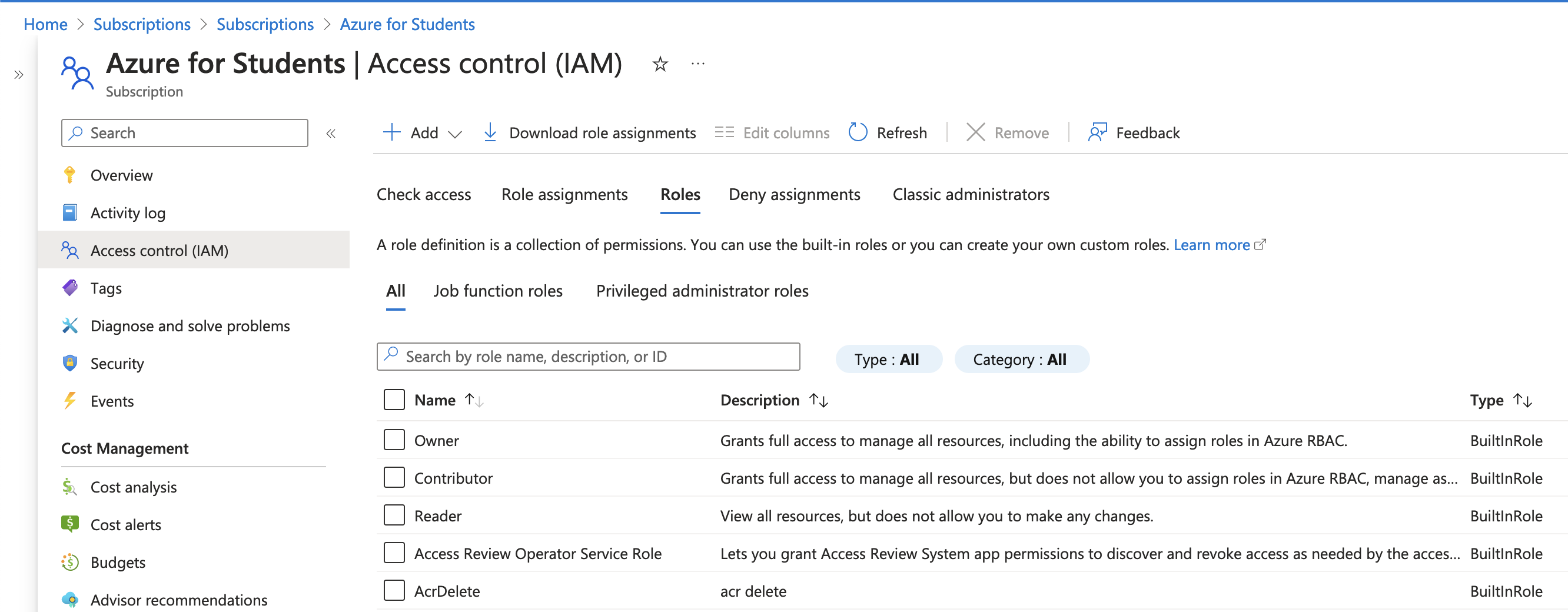
- Click on "+ Add" and select "Add role assignment"
- In the search bar, type
Security Reader, select it and click on "Next" - In the Members tab, click on "+ Select members" and add the members you want to assign this role.
- Click on "Review + assign" to apply the new role.
Repeat these steps for Reader role
Google Cloud¶
Authentication¶
Prowler will follow the same credentials search as Google authentication libraries:
- GOOGLE_APPLICATION_CREDENTIALS environment variable
- User credentials set up by using the Google Cloud CLI
- The attached service account, returned by the metadata server
Those credentials must be associated to a user or service account with proper permissions to do all checks. To make sure, add the Viewer role to the member associated with the credentials.
Note
By default, prowler will scan all accessible GCP Projects, use flag --project-ids to specify the projects to be scanned.